Newsletter #3 2024
Published on: February 11, 2024
Hi,
First of all, thank you for subscribing and reading the EndpointCave security newsletter.
I feel honored that you will join me on the journey of this bi-weekly Security Newsletter! My goal is to deliver valuable security content directly to you and your inbox.
But I need your help, do you have any valuable content that needs to be shared with the community? Did you create a security blog post or did you find a security-related news item that needs to be mentioned in my upcoming newsletters?
Please send me a message. You can contact me on X (Twitter) or LinkedIn.
The community has created a lot of content. In this newsletter, I reviewed about 200 items, I selected 25 community blogs and 4 videos. I also highlighted the following 3 items:
- Still, granting Graph API permissions to non-human entities to access Exchange Online resources?
- Entra ID Governance Training
- Differences between Microsoft Defender for Cloud Apps and Microsoft 365 Cloud App Security?
Enjoy
Highlights
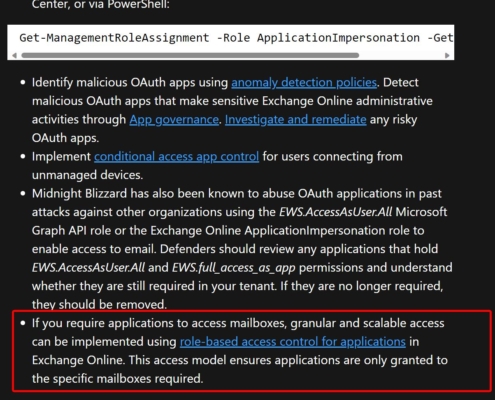
Still, granting Graph API permissions to non-human entities to access Exchange Online resources?
If you still grant Graph API permissions to non-human identities to access Exchange Online resources, please consider moving to Role Based Access Control for Applications in Exchange Online instead. It’s more granular and scalable than giving out mail.read/write.all, giving access to ALL mailboxes.
If we look at the latest hack at Microsoft, this is one of the lessons we can take from that. https://lnkd.in/e-mF5Qjv
Jan Bakker has written a blog post about it to raise awareness: Check out his blogpost here
Entra ID Governance Training
This GitHub repository is dedicated to Entra Identity Governance – a comprehensive resource hub designed to guide you through the intricacies of managing identities effectively. Whether you’re a seasoned professional or just starting, here you’ll find the tools, documentation, and training materials to master the art of identity governance.
More information: Click here
Differences between Microsoft Defender for Cloud Apps and Microsoft 365 Cloud App Security?
5 main differences in capability:
▪ Cloud Discovery
▪ Information Protection
▪ Threat Detection
▪ Conditional Access App Control
▪ Cloud Platform Security
More information: Click here
Security topics to watch
Power Platform Activity Logging In Microsoft Purview
Power Platform Activity Logging In Microsoft Purview.
Microsoft Purview provides detailed logs about Power Platform that you need to police the activity. This cannot be done via the existing Power Platform Center of Excellence (CoE) Tool and hence it is important to consider leveraging this feature. In this video I will walk you through where in Microsoft Purview this feature is available, how to use it, and then do a side-by-side comparison with Power Platform’s CoE tool.
A New Approach to Get Your Cloud Risks Under Control
Oz Wilder (Director of Product – Microsoft Defender for Cloud) and Dr. Tamer Salman (Head of Research – Microsoft Defender for Cloud) share a new approach to get your cloud risks under control. We were platinum sponsors at the SANS 2023 Multicloud Survey: Navigating the Complexities of Multiple Clouds. Multicloud adoption will continue to increase as organizations require increased agility, flexibility, choice, and scalability.
Recommendation Prioritization | Defender for Cloud in the Field #45
In this episode of Defender for Cloud in the Field, Aviram Yitzhak joins Yuri Diogenes to talk about recommendation prioritization in Microsoft Defender for Cloud. Aviram explains the correlation between recommendation prioritization and attack path, and when to use each dashboard. Aviram also demonstrates the user experience when using recommendation prioritization dashboard to triage recommendations based on risk factors.
MS Purview Customer Network Monthly Meeting Series
In the February monthly call from Microsoft Purview Customer Network community I was invited to talk about MPARR, please review the recorded session where I was talking in general about MPARR but adiitionally, they are talking about new features, new reports and new things that I’m adding to our roadmap. I hope that you can enjoy this session.
Blogs from the community
This is the end of this newsletter. Thank you for reading the Endpoint Security newsletter, I hope you have found valuable content that you can use.
Do you have any feedback? Please feel free to share your thoughts and suggestions with me for future editions. Any valuable content of blogs that I need to monitor or share. Please send me a message. You can contact me on X (Twitter) or LinkedIn.
Kind Regards,
René Laas – MVP
EndpointCave

 Hi! My name is René Laas. I have passion and enthusiasm for the Microsoft 365 Cloud. I am based in the Netherlands.
Hi! My name is René Laas. I have passion and enthusiasm for the Microsoft 365 Cloud. I am based in the Netherlands.
 Andrea De Santis
Andrea De Santis