Configure ASR Rules via Endpoint Security with Microsoft Intune
The purpose of this blog post is to inform you how to configure Attack Surface Reduction Rules (ASR) via Endpoint Security Profiles with Microsoft Intune
There are several options to configure Attack Surface Reduction Rules, in my previous blog post I have explained how to configure if via custom configuration, during the creation of the blog post, not all ASR rules were configurable via the Endpoint security blade, filters were not configurable or not all ASR rules were configurable in a configuration profile or security baseline. With a Custom configuration profile, I was able to use filters and set all ASR Rules in one profile. Microsoft is constantly updating Microsoft Endpoint Manager and today it is possible to set all ASR rules via a Custom configurations and Endpoint Security ASR profile.
So in this blog post I will explain the Endpoint Security option.
Basic requirements:
Extensive requirements: (Entire feature set of ASR rules)
Note. With a Windows E5 license, you get advanced management capabilities including monitoring, analytics, and workflows available in Defender for Endpoint, as well as reporting and configuration capabilities in the Microsoft 365 Defender portal.
What are Attack Surface Reduction rules?
Attack surfaces are all the places where your organization is vulnerable to cyber threats and attacks. An attacker could compromise your organization’s devices or networks. To minimize the risk that an attacker could compromise your device, you must implement security measures e.g., Attack Surface Reduction rules, Network protection, application control, etc. See Microsoft documentation for all the security measures.
So, Attack Surface Reduction rules are settings that make your device better protected against attacks and odd behavior. Attack Surface Reduction protects you e.g., against potentially obfuscated scripts or credentials stealing from Windows local security authority subsystem (LSASS).
Configuration possibilities
There are several options available to configure the Attack Surface Reduction rules. Within Microsoft Intune, you have five options to configure ASR rules.
- Attack Surface Reduction Rules via Endpoint protection
Endpoint protection configuration profile can be used to control the security of Windows devices. The category Microsoft Defender Exploit Guard contains an Attack Surface Reduction group and contains nearly all currently available ASR rules.
- Attack Surface Reduction Rules via custom configuration profile
A custom configuration profile can be used to configure settings that are available in Configuration Service Provider (CSP). CSP also includes all ASR rules. ASR rules and exclusions need to be set via custom OMA-URI’s.
- Attack Surface Reduction Rules via MDM Security Baseline
Security baselines are Microsoft-recommended configuration settings. These settings are based on feedback from Microsoft security engineering teams, product groups, partners, and customers. A security baseline includes a group of Microsoft Defender settings. The Security Baseline contains nearly all currently available ASR rules.
- Attack Surface Reduction Rules via Endpoint Security Attack Surface Reduction rules
The Attack Surface Reduction rules profile can be used to configure the Attack Surface Reduction rules and contains nearly all currently available ASR rules.
- Attack Surface Reduction Rules via PowerShell script
PowerShell is a cross-platform task automation solution made up of a command-line shell, a scripting language, and a configuration management framework. We can use a PowerShell script to set all the available ASR rules.
PowerShell command for e.g., Block abuse of exploited vulnerable signed drivers:
Add-MpPreference -AttackSurfaceReductionRules_Ids 56a863a9-875e-4185-98a7-b882c64b5ce5 -AttackSurfaceReductionRules_Actions EnabledWhich option should I use?
Depending on the organization’s preferences, As you can see in the above paragraph there are several methods to set the ASR rules. I always advise people to keep all the configurations for a same feature/topic in one profile, so all ASR rules are in one configuration profile, all BitLocker settings in one configuration profile etc.
The easiest way is to configure ASR rules is the endpoint security Attack Surface Reduction rules profile and change all the other ASR rules settings in e.g., Security baseline to not configure. If you don’t change the settings to not configure, you can get profile conflicts and ASR will not be applied well.
More information about Policy conflicts: Troubleshoot device profiles in Microsoft Intune | Microsoft Learn
The endpoint Protection profiles, and the Microsoft Security baseline does not have all the ASR rules available in their profiles, you cannot set the missing rules via a Custom configuration profile because it will overrule each other constantly. From my opinion the Security baseline and Endpoint Protection Profiles are not the right option to use.
So, we have the Custom configuration profile, PowerShell and Endpoint security ASR profiles left. You can set the Profiles via a PowerShell command, but the disadvantage of PowerShell command is that when it is set it will never revert to the default when you unassign the PowerShell script and the report of the PowerShell scripts is not the best report. It will only report if your script has run successfully or failed.
The last 2 options are Custom configuration profiles and Endpoint Security ASR profiles. Both profiles support filters and all ASR rules can be set. Custom configuration profiles can set the ASR rules via OMA-URI, most of the admin does not understand OMA-URI’s and are harder to read, the report is limited to see only if the profile is successfully applied on the device. Endpoint Security has a more friendly user interface within the Microsoft Endpoint Manager portal and report functionality, So, that is the reason why I prefer to use the Endpoint Security profile.
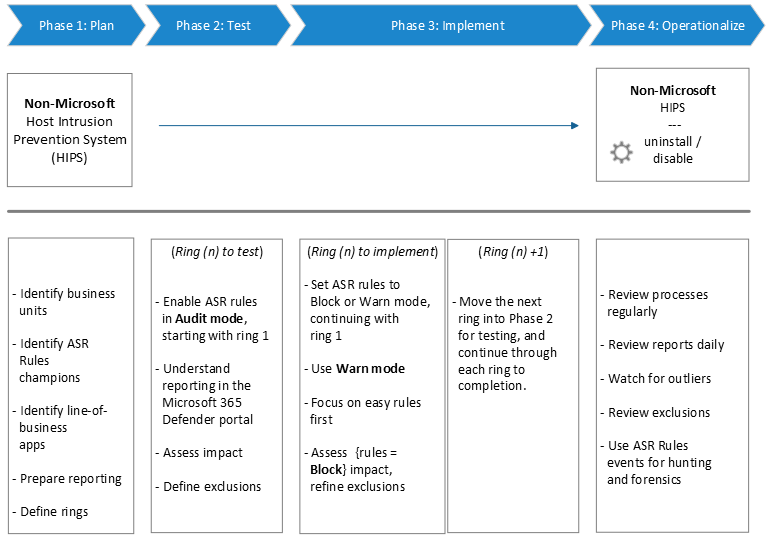
Attack Surface Reduction rules deployment phases
As with any new, wide-scale implementation which could potentially impact your line-of-business operations, it is important to be methodical in your planning and implementation. Because of the powerful capabilities of ASR rules in preventing malware, careful planning and deployment of these rules are necessary to ensure they work best for your unique customer workflows. To work in your environment, you need to plan, test, implement, and operationalize ASR rules carefully.
Attack Surface Reduction Profiles
| GUID | Attack surface reduction (ASR) rules |
|---|---|
| 75668c1f-73b5-4cf0-bb93-3ecf5cb7cc84 | Block Office applications from injecting code into other processes |
| 3b576869-a4ec-4529-8536-b80a7769e899 | Block Office applications from creating executable content |
| d4f940ab-401b-4efc-aadc-ad5f3c50688a | Block all Office applications from creating child processes |
| 26190899-1602-49e8-8b27-eb1d0a1ce869 | Block Office communication application from creating child processes |
| 92e97fa1-2edf-4476-bdd6-9dd0b4dddc7b | Block Win32 API calls from Office macros |
| 5beb7efe-fd9a-4556-801d-275e5ffc04cc | Block execution of potentially obfuscated scripts |
| d3e037e1-3eb8-44c8-a917-57927947596d | Block JavaScript or VBScript from launching downloaded executable content |
| 9e6c4e1f-7d60-472f-ba1a-a39ef669e4b2 | Block credential stealing from the Windows local security authority subsystem (lsass.exe) |
| d1e49aac-8f56-4280-b9ba-993a6d77406c | Block process creations originating from PSExec and WMI commands |
| b2b3f03d-6a65-4f7b-a9c7-1c7ef74a9ba4 | Block untrusted and unsigned processes that run from USB |
| 01443614-cd74-433a-b99e-2ecdc07bfc25 | Block executable files from running unless they meet a prevalence, age, or trusted list criterion |
| be9ba2d9-53ea-4cdc-84e5-9b1eeee46550 | Block executable content from email client and webmail |
| c1db55ab-c21a-4637-bb3f-a12568109d35 | Use advanced protection against ransomware |
| 7674ba52-37eb-4a4f-a9a1-f0f9a1619a2c | Block Adobe Reader from creating child processes |
| e6db77e5-3df2-4cf1-b95a-636979351e5b | Block persistence through WMI event subscription |
| 56a863a9-875e-4185-98a7-b882c64b5ce5 | Block abuse of exploited vulnerable signed drivers |
How to configure the ASR rules
- Open Microsoft endpoint manager
- In the menu select Endpoint Security
- In the second menu click on attack surface reduction
Or use the following Link: Endpoint security – Microsoft Endpoint Manager admin center
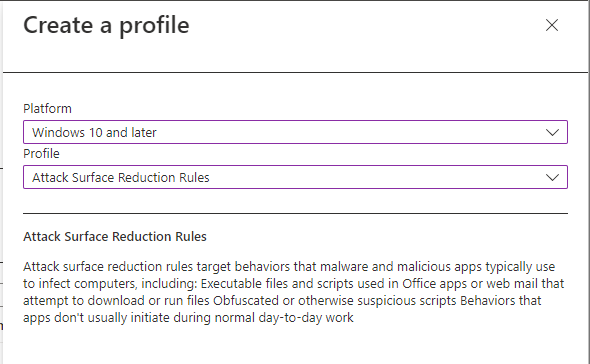
- Click on + Create Policy
- Select Windows 10 and later as the platform
- Set Attack Surface Reduction Rules as the profile
- Click on Create
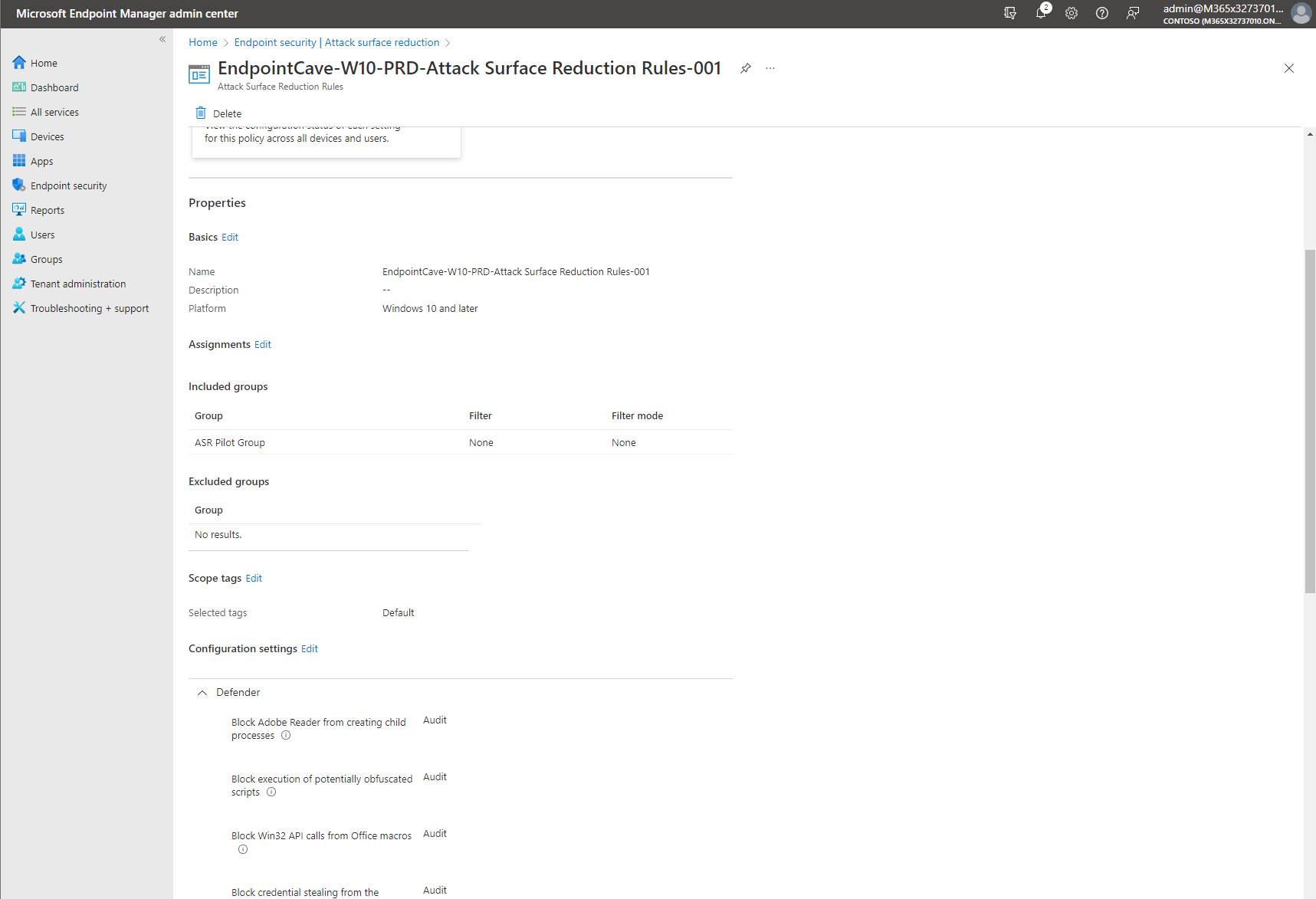
- Provide a policy name, e.g., EndpointCave-W10-PRD-Attack Surface Reduction Rules-001
- Set a Description, so that everyone with access to the portal knows the purpose
- Click on Next
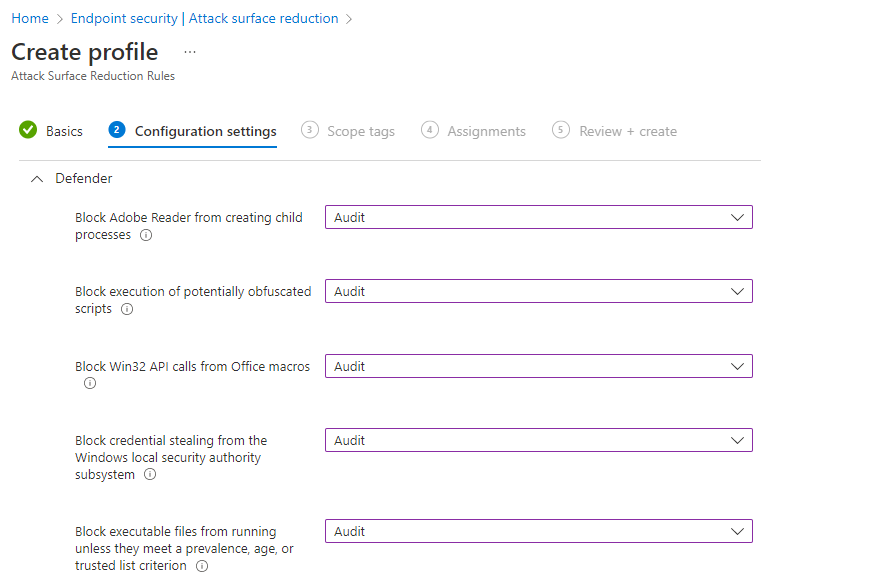
- Set all setting to the right configuration. My advice is to start with audit mode as explained in Attack Surface Reduction rules deployment phases.
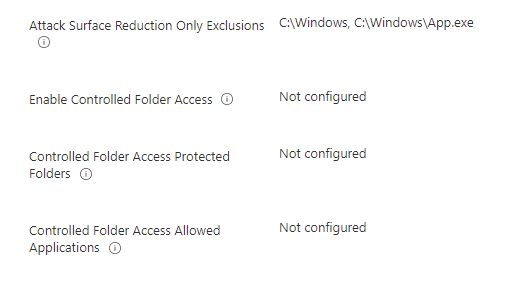
- Leave Attack Surface Reduction Only Exclusion, enable controlled folder access, Controlled Folder Access Protected Folders, and Controlled Folder Access Allowed Applications as not configured
- Click on Next
- Enter a scope tag if needed and click on Next
- Assign the profile to a pilot group and click on Next
- Check the configuration at the Review + Create page and click on Create
How to configure an ASR Exclusion
- Open Microsoft endpoint manager
- In the menu select Endpoint Security
- In the second menu click on attack surface reduction
Or use the following Link: Endpoint security – Microsoft Endpoint Manager admin center - Open an ASR Rule, eg., EndpointCave-W10-PRD-Attack Surface Reduction Rules-001
- Scroll down to the Configuration settings and click on Edit
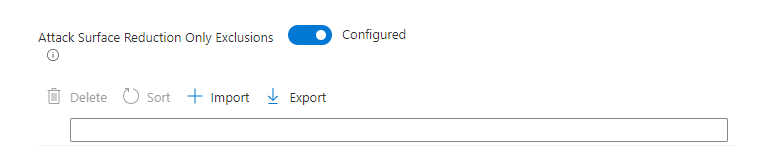
- Go to the Attack Surface Reduction Only Exclusions setting
- Click on the toggle to enable the exclusion setting
- Enter an exclusion path or fully qualified resource path. e.g., a path might be defined as: c:\Windows to exclude all files in this directory. A fully qualified resource name might be defined as: C:\Windows\App.exe.
Note. Exclusions will affect every ASR rule. But not all ASR rules support exclusions. The following rules don’t support exclusions:
- Block persistence through WMI event subscription
- Block JavaScript or VBScript from launching downloaded executable content
- For another exclusion, use the second input field
- After you add all exclusions click on Review + save
- Check the configuration at the Review + Create page and click on Save
Test your Attack surface reduction rules
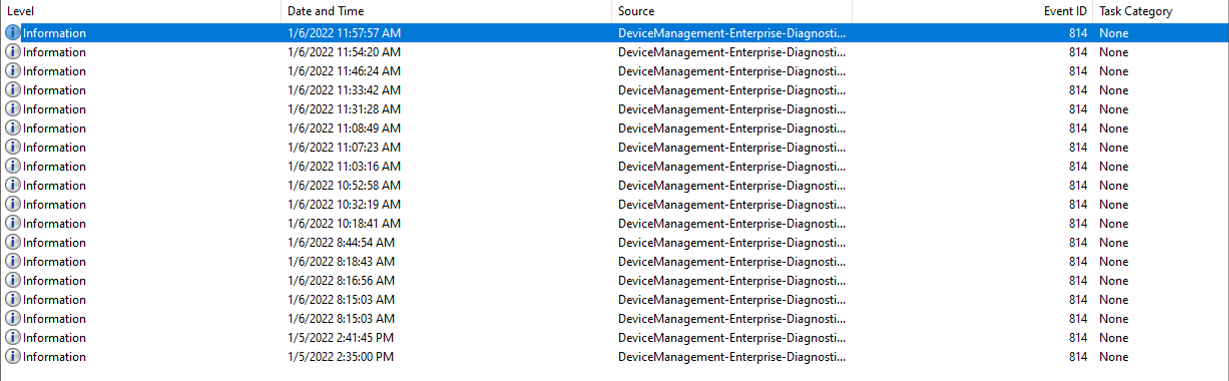
If you assigned the ASR rules to a user or device and are successfully applied on the Windows device. You can use the Event viewer to check what is applied.
The DeviceManagement-Enteprise-Diagnostics-Provide -> Admin log file can be used to check the applied configurations. The log includes the ASR rules configuration. A successful configuration will show as Event ID 814.
You can also get a detailed report with ASR rules events, blocks, and warnings if you have an E5 subscription and use Microsoft Defender for Endpoint.


 Hi! My name is René Laas. I have passion and enthusiasm for the Microsoft 365 Cloud. I am based in the Netherlands.
Hi! My name is René Laas. I have passion and enthusiasm for the Microsoft 365 Cloud. I am based in the Netherlands. Monstera
Monstera Matthew Jungling
Matthew Jungling
Leave a Reply
Want to join the discussion?Feel free to contribute!